Google Professional Security Operations Engineer

The Google Cloud Certified – Professional Security Operations Engineer certification validates advanced expertise in protecting cloud-based and hybrid enterprise environments using Google’s security ecosystem. This role focuses on identifying, analyzing, and responding to security threats across workloads, endpoints, networks, and cloud infrastructure with a strong emphasis on operational security at scale.
A certified Security Operations Engineer is expected to actively monitor security signals, investigate suspicious activity, and coordinate effective responses using Google Cloud security services. The role goes beyond basic alert handling and requires a deep understanding of how telemetry, automation, and intelligence-driven detection work together in modern security operations.
Role and Responsibilities
Professionals pursuing this certification are responsible for designing and operating security detection and response workflows within Google Security Operations (SecOps) and Security Command Center (SCC). This includes building detection logic, managing and prioritizing logs, automating response actions, and continuously improving security posture using real-world threat intelligence.
Candidates should be comfortable working with large volumes of security data and turning that data into actionable insights. The role also requires close collaboration with incident response teams, cloud engineers, and compliance stakeholders to ensure threats are detected early and handled efficiently.
Skills and Capabilities Assessed
The exam evaluates a candidate’s ability to perform core security operations tasks in a Google Cloud environment, including:
- Platform Operations
- Managing and operating Google security platforms to ensure reliable ingestion, processing, and availability of security data across the organization.
- Data Management
- Handling log collection, normalization, enrichment, and retention strategies to support effective detection and investigation workflows.
- Threat Hunting
- Proactively searching for indicators of compromise and abnormal behavior using hypothesis-driven techniques and historical security data.
- Detection Engineering
- Designing, tuning, and maintaining detection rules that balance accuracy and coverage while minimizing false positives.
- Incident Response
- Investigating alerts, determining root cause, coordinating containment actions, and automating response workflows where appropriate.
- Observability
- Maintaining visibility across cloud resources, services, and user activity to ensure security signals are not missed and system behavior is well understood.
Tools and Technologies in Scope
The certification heavily emphasizes hands-on knowledge of Google Security Operations (SecOps) for SIEM and SOAR capabilities, along with Security Command Center (SCC) for posture management, vulnerability findings, and threat detection. Candidates are expected to understand how these tools integrate with Google Cloud services and external data sources to create a unified security operations workflow.
Recommended Experience
Google recommends that candidates have at least three years of professional experience in the cybersecurity field, with a minimum of one year working directly with Google Cloud security tools. Practical exposure to real-world incidents, detection tuning, and security automation is highly beneficial for success in the exam.
Who Should Take This Exam
This certification is ideal for security analysts, SOC engineers, cloud security engineers, and incident response professionals who are responsible for defending cloud-based environments. It is particularly valuable for individuals working in organizations that rely on Google Cloud or are transitioning their security operations to cloud-native platforms.
Exam Details
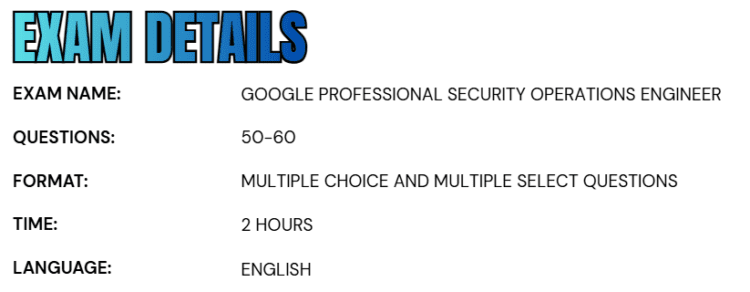
- The Google Cloud Certified – Professional Security Operations Engineer exam is a two-hour assessment designed to evaluate a candidate’s ability to perform advanced security operations tasks in a Google Cloud environment.
- The exam is conducted entirely in English and consists of approximately 50 to 60 multiple-choice and multiple-select questions, requiring both conceptual understanding and practical decision-making skills.
- Candidates can choose from two exam delivery options based on their preference and convenience.
- The exam may be taken as an online-proctored test from a remote location, provided all technical and identity verification requirements are met. Alternatively, candidates may opt for an onsite-proctored exam at an authorized testing center, allowing them to take the test in a controlled, in-person environment.
Course Outline
The Google Cloud Certified – Professional Security Operations Engineer exam covers the following topics:
Section 1: Understand Platform operations (14%)
1.1 Enhancing detection and response. Considerations include:
- Prioritizing telemetry sources (e.g., Security Command Center [SCC], Google Security Operations [SecOps], GTI, Cloud IDS) to detect incidents or miscongurations within an enterprise environment
- Integrating multiple tools (e.g., SCC, Google SecOps, GTI, Cloud IDS, downstream third-party system) in the security architecture to enhance detection capabilities
- Justifying the use of tools with overlapping capabilities based on a set of requirements
- Evaluating the eectiveness of existing tools to identify gaps in coverage and mitigate potential threats
- Evaluating automation and cloud-based tools to enhance existing detection and response processes
1.2 Configuring access. Considerations include:
- Configuring user and service account authentication to security tools (e.g., SCC, Google SecOps)
- Configuring user and service account authorization for feature access using IAM roles and permissions
- Configuring user and service account authorization for data access using IAM roles and permissions
- Configuring and analyzing audit logs (e.g., Cloud Audit Logs, data access logs) for the solution
- Configuring API access for automations within security tools (e.g., service accounts, API keys, SCC, Google SecOps, GTI)
- Provisioning identities using Workforce Identity Federation
Section 2: Learn About Data Management (14%)
2.1 Ingesting logs for security tooling. Considerations include:
- Determining approaches for data ingestion within security tools (e.g., SCC, Google SecOps)
- Configuring an ingestion tool or features within security tools (e.g., SCC, Google SecOps)
- Assessing required logs for detection and response, including automated sources, within security tools (e.g., SCC Event Threat Detection, Google SecOps)
- Evaluating parsers for data ingestion in Google SecOps
- Configuring parser modifications or extensions in Google SecOps
- Evaluating data normalization techniques from log sources in Google SecOps
- Evaluating new labels for data ingestion
- Managing log and ingestion costs
2.2 Identifying a baseline of user, asset, and entity context. Considerations include:
- Identifying relevant threat intelligence information in the enterprise environment
- Differentiating event and entity data log sources (e.g., Cloud Audit Logs, Active Directory organizational context)
- Evaluating event and entity data matches for enrichment by using aliasing elds
Section 3: Understand Threat hunting (19%)
3.1 Performing threat hunting across environments. Considerations include:
- Developing queries to search across environment logs to identify anomalous activity
- Analyzing user behavior to identify anomalous activity
- Investigating the network, endpoints, and services to identify threat patterns or indicators of compromise (IOCs) using Google Cloud tools (e.g., Logs Explorer, Log Analytics, BigQuery, Google SecOps)
- Collaborating with the incident response team to identify active threats in the environment
- Developing hypotheses based on behavior, threat intel, posture, and incident data (e.g., SCC, GTI)
3.2 Leveraging threat intelligence for threat hunting. Considerations include:
- Searching for IOCs within historical logs
- Identifying new attack patterns and techniques in real time using threat intelligence and risk assessments (e.g., GTI, detection rules, SCC toxic combinations)
- Analyzing entity risk score to identify anomalous behavior
- Comparing and performing retrohunt of historical event data with newly enriched logs (e.g., Google SecOps rules engine, BigQuery, Cloud Logging)
- Searching proactively for underlying threats using threat intelligence (e.g., GTI, detection rules)
Section 4: Overview of Detection Engineering (22%)
4.1 Developing and implementing mechanisms to detect risks and identify threats. Considerations include:
- Reconciling threat intelligence with user and asset activity
- Analyzing logs and events to identify anomalous activity
- Assessing suspicious behavior patterns by using detection rules and searches across various timelines
- Designing detection rules that use risk values (e.g., Google SecOps reference lists) to identify threats matching risk proles
- Discovering anomalous behavior of assets or users, and assigning risk values to the detections (e.g., Google SecOps Risk Analytics, curated detection rules)
- Designing detection rules to discover posture or risk profile changes within the environment (e.g., SCC Security Health Analytics [SHA], SCC posture management, Google SecOps)
- Identifying new or low-prevalence processes, domains, and IP addresses that do not appear in threat intelligence sources using various methods (e.g., writing YARA-L rules, dashboards)
- Assessing how to use entity/context data within detection rules to improve their accuracy (e.g., Google SecOps entity graph)
- Configuring SCC Event Threat Detection custom detectors for IOCs
4.2 Leveraging threat intelligence for detection. Considerations include:
- Scoring alerts based on the risk level of IOCs
- Using the latest IOCs to search within ingested security telemetry
- Measuring the frequency of repetitive alerts to identify and reduce false positives
Section 5: Understand Incident response (21%)
5.1 Containing and investigating security incidents. Considerations include:
- Collecting evidence on the scope of the incident, including forensic images and artifacts
- Observing and analyzing alerts related to the incident using security tooling (e.g., SCC, Google SecOps)
- Analyzing the scope of the incident using security tooling (e.g., Logs Explorer, Log Analytics, BigQuery, Cloud Logging, Cloud Monitoring)
- Collaborating with other engineering teams for detection and long-term remediation efforts
- Isolating affected services and processes to prevent further damage and spread of aack
- Analyzing identified artifacts based on forensic analysis (e.g., Hash, IP, URL, Binaries) (GTI)
- Performing root cause analysis using security tools (e.g., SCC, Google SecOps SIEM)
5.2 Building, implementing, and using response playbooks. Considerations include:
- Determining the appropriate response steps for automation
- Prioritizing high-value enrichments based on threat proles
- Evaluating appropriate integrations to be leveraged by playbooks
- Designing new processes in response to newly identified attack patterns from recent incidents
- Recommending new orchestrations and automation playbooks based on gaps in the current implementation (e.g., Google SecOps SOAR)
- Implementing mechanisms to notify analysts and stakeholders of incidents
5.3 Implementing the case management lifecycle. Considerations include:
- ● Assigning cases into appropriate response stages
- ● Implementing efficient workflows for case escalation
- ● Assessing the effectiveness of case handoffs
Section 6: Observability (10%)
6.1 Developing and maintaining dashboards and reports to provide insights. Considerations include:
- Identifying key security analytics (e.g., metrics, KPIs, trends)
- Implementing dashboards to visualize security telemetry, ingestion metrics, detections, alerts, and IOCs (e.g., Google SecOps SOAR, SIEM, Looker Studio)
- Generating and customizing reports (e.g., Google SecOps SOAR, SIEM)
6.2 Configuring health monitoring and alerting. Considerations include:
- Identifying important metrics for health monitoring and alerts
- Creating dashboards that centralize metrics
- Creating alerts with thresholds for specific metrics
- Configuring notifications using Google Cloud tools (e.g., Cloud Monitoring)
- Identifying health issues using Google Cloud tools (e.g., Cloud Logging)
- Configuring silent source detection
Google Professional Security Operations Engineer Exam FAQs
Exam Policies
Understanding Google Cloud certification policies is essential before scheduling or renewing your exam. These policies outline procedures for rescheduling, cancellations, and certification renewal to ensure a smooth certification experience.
Rescheduling or Canceling an Exam
If you need to modify your exam appointment, you must access your certification account through CM Connect and launch Webassessor. From the “My Assessments” section, you can choose to reschedule or cancel your existing booking. Be mindful of the timing when making changes. For exams scheduled at a physical testing center, a late fee will apply if you reschedule or cancel less than 72 hours before the scheduled start time. For remotely proctored online exams, the late change window is shorter—fees apply if adjustments are made within 24 hours of the exam appointment. Planning ahead helps avoid unnecessary penalties.
Certification Renewal
Google Cloud certifications are valid for a limited period, reflecting the rapidly evolving nature of cloud technologies. To maintain an active certification status and retain your original certificate identifier (Series ID), you must complete the recertification process during the designated renewal window. The renewal eligibility window depends on the certification level:
- Foundational and Associate certifications: Renewal can begin up to 180 days before the expiration date.
- Professional certifications: Renewal can begin up to 60 days before the expiration date.
Attempting to renew before your official eligibility window may result in rejection of the attempt, and exam fees may not be refunded. Standard exam fees and retake policies apply to all renewal attempts.
Google Professional Security Operations Engineer Exam Study Guide
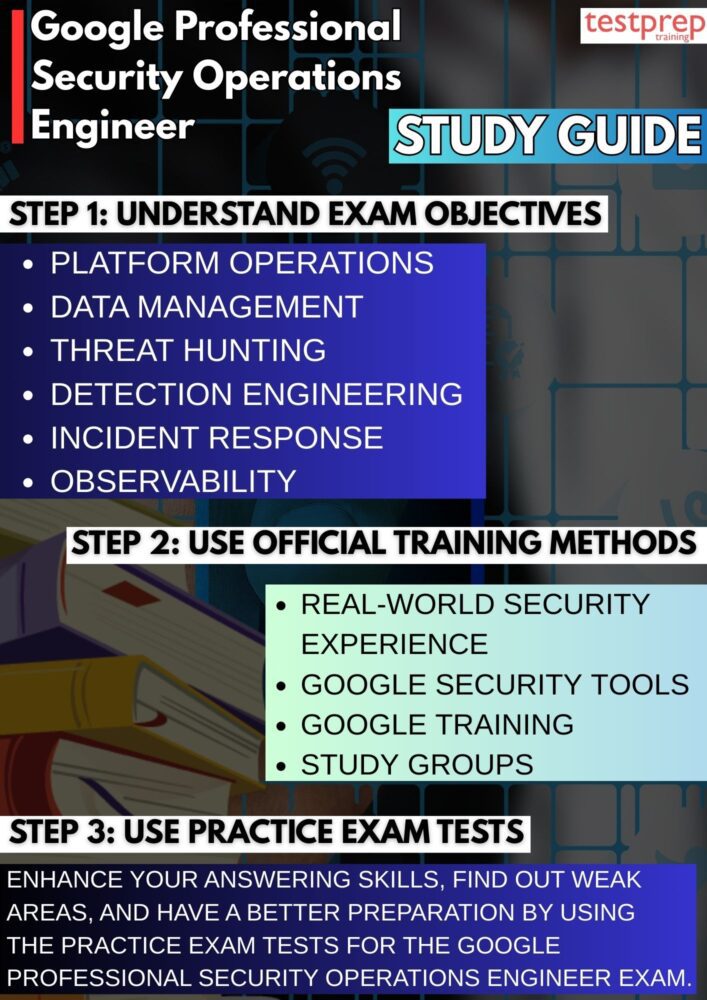
1. Understanding the Exam Scope and Objectives
The first step in preparation is to thoroughly review the official exam guide and understand the domains being assessed. The certification focuses on areas such as platform operations, data management, threat hunting, detection engineering, incident response, and observability. Rather than treating these domains as separate topics, candidates should understand how they function together within a complete security operations lifecycle. For example, effective threat detection relies on properly ingested and normalized logs, while incident response depends on accurate alerting and investigation workflows.
A deep understanding of the exam blueprint allows candidates to align their preparation with the competencies being evaluated. It also helps identify weaker areas that require additional focus before scheduling the exam.
2. Building and Evaluating Real-World Security Experience
Because this is an advanced certification, practical experience plays a critical role in exam readiness. Google recommends that candidates have at least three years of experience in cybersecurity roles, along with a minimum of one year working directly with Google Cloud security tools. The exam scenarios are designed to test applied knowledge rather than memorized facts, so familiarity with real-world detection, investigation, and response processes significantly improves performance.
Candidates should reflect on their hands-on experience in areas such as writing detection rules, analyzing logs, triaging alerts, and coordinating response efforts. If gaps exist, it is advisable to strengthen those areas through lab simulations or structured practice before attempting the exam.
3. Gaining Hands-On Experience with Google Security Tools
Practical exposure to Google Security Operations (SecOps) and Security Command Center (SCC) is essential. Candidates should be comfortable navigating these platforms, understanding how security findings are generated, and interpreting threat intelligence signals. Working directly with log ingestion pipelines, query building, alert tuning, and automation workflows helps build operational confidence.
Hands-on practice should also include understanding how automation and orchestration can streamline incident response. Familiarity with how security telemetry is collected, enriched, and correlated within Google Cloud environments enables candidates to approach scenario-based questions with clarity and technical accuracy.
4. Leveraging Official Google Cloud Training Resources
Structured learning through Google Cloud’s official training materials provides alignment with exam objectives and current platform capabilities. Candidates should explore available online courses, instructor-led sessions, documentation, architecture guides, and hands-on labs. Official documentation is particularly valuable because it reflects real implementation standards and best practices.
Studying architecture patterns, security frameworks, and operational best practices deepens conceptual understanding and prepares candidates to make informed decisions in complex exam scenarios. Combining documentation study with practical experimentation creates a balanced preparation strategy.
5. Engaging with Study Groups and Professional Communities
Participating in professional communities can significantly enhance preparation. Engaging with peers who are also preparing for the exam encourages knowledge sharing and exposes candidates to different perspectives on detection strategies and incident response workflows. Discussions within cloud security forums, LinkedIn groups, or technical communities often surface practical insights that may not be covered in formal documentation. Collaborative learning helps reinforce key concepts and improves problem-solving abilities, particularly for scenario-based questions that require critical thinking.
6. Practicing with Scenario-Based Exams and Mock Tests
Practice exams are an important component of preparation for a professional-level certification. The Google Professional Security Operations Engineer exam includes multiple-choice and multiple-select questions that often present detailed enterprise scenarios. These questions require candidates to evaluate multiple factors, such as scalability, efficiency, automation, and security best practices, before selecting the most appropriate solution.
Taking mock exams under timed conditions improves time management and builds confidence. Reviewing explanations for both correct and incorrect answers helps identify knowledge gaps and strengthens conceptual clarity. Repeated practice ensures readiness for the exam’s complexity and structure.
7. Final Review and Exam Strategy
In the final phase of preparation, candidates should focus on consolidating their understanding of core workflows, including detection logic, investigation procedures, automation strategies, and incident response lifecycle stages. Rather than attempting to learn entirely new topics at the last minute, the emphasis should be on refining existing knowledge and strengthening weaker areas.
Developing a clear exam strategy is equally important. Carefully reading each question, identifying key technical requirements, and distinguishing between similar answer choices can prevent avoidable mistakes. With thorough preparation, practical experience, and a structured review process, candidates can approach the exam with confidence and a strong operational mindset.