Splunk Certified Cybersecurity Defense Engineer (SPLK-5002)

The Splunk Certified Cybersecurity Defense Engineer certification is designed to validate advanced, job-ready skills required to operate and enhance modern Security Operations Centers (SOCs). This exam focuses on how professionals use Splunk technologies to strengthen detection capabilities, streamline response workflows, and implement automation aligned with real-world security best practices.
By earning this certification, candidates demonstrate their ability to design, tune, and maintain effective security detections, integrate risk-based approaches, and build scalable automation that improves SOC efficiency and consistency.
Further, this certification signals that you are capable of contributing at a higher strategic and technical level within a SOC. It demonstrates your readiness to design resilient detection strategies, automate repeatable workflows, and support security operations with scalable, well-governed solutions—key capabilities for long-term growth in cybersecurity defense engineering.
What This Exam Validates
This certification confirms your readiness to progress into a Cybersecurity Defense Engineering role by assessing your ability to:
- Analyze security threats, vulnerabilities, and attack patterns within a SOC environment
- Create, refine, and optimize detections to reduce noise and improve signal quality
- Apply risk-based principles to prioritize alerts and response actions
- Develop and follow structured security processes and operational programs
- Automate standard operating procedures to enhance response speed and reliability
Recommended Knowledge and Experience
There are no mandatory prerequisite certifications for this exam. However, candidates are strongly advised to have:
- Power User–level proficiency with Splunk Enterprise
- Working familiarity with administrative concepts in Splunk Cloud or Splunk Enterprise
- A foundational understanding of SOC workflows, alert triage, and incident response
Who Should Take This Exam?
The exam is for:
- Splunk Certified Cybersecurity Defense Analysts
- Professionals who already work in detection and analysis roles and want to advance into a defense engineering career path will find this certification a natural next step.
- SOC Detection Engineers
- Engineers responsible for building, tuning, and maintaining detections can use this certification to formally validate their expertise in optimizing detection logic and automation.
- Cybersecurity Professionals
- SOC analysts and security practitioners looking to deepen their technical impact can leverage this certification to transition into more advanced, engineering-focused roles.
- Career Builders
- This certification supports professionals aiming to strengthen their credentials and stand out as trusted security engineers within organizations using Splunk technologies.
Exam Details
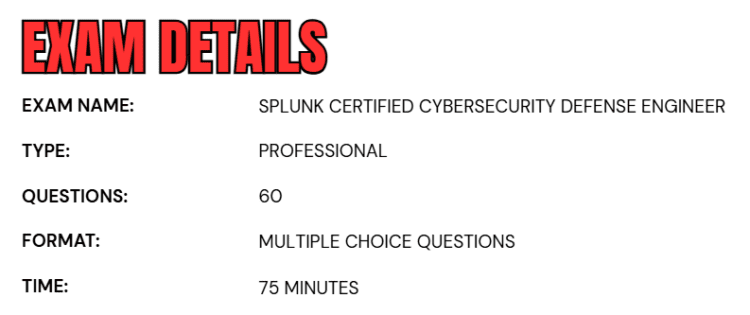
- The Splunk Certified Cybersecurity Defense Engineer exam is a professional-level certification assessment designed to evaluate advanced competencies in cybersecurity defense engineering.
- The exam is 75 minutes in duration and consists of 60 multiple-choice questions that measure a candidate’s ability to apply Splunk-based detection, automation, and SOC engineering concepts in real-world scenarios.
- The examination is administered through Splunk’s official testing partner, Pearson VUE, ensuring a standardized and secure certification experience.
Course Outline
The Splunk Certified Cybersecurity Defense Engineer exam covers the following topics:
1. Overview of Data Engineering 10%
- Performing effective data review and analysis.
- Creating and maintaining performant data indexing.
- Understanding and applying Splunk methods of data normalization.
2. Learn Detection Engineering 40%
- Creating and tuning detections (i.e. Correlation Search).
- Incorporating context into detections (i.e. Correlation Search).
- Understanding and creating risk-based modifiers and detections.
- Generating effective Notable Events/findings.
- Creating and maintaining a detection lifecycle.
3. Methods for Building Effective Security Processes and Programs 20%
- Researching, incorporating and developing threat intelligence.
- Using common methodologies for risk and detection prioritization.
- Generating documentation and standard operating procedures.
4. Understand Automation and Efficiency 20%
- Developing automation and orchestration for standard operating procedures.
- Optimizing Case Management.
- Describing and utilizing REST APIs.
- Automating responses using SOAR playbooks.
- Comparing and validating integrations and automation capabilities of Enterprise Security and SOAR.
5. Learn Auditing and Reporting on Security Programs 10%
- Developing and optimizing security metrics.
- Building and populating effective security reports.
- Building and populating dashboards for program analytics.
Splunk Certified Cybersecurity Defense Engineer (SPLK-5002) Exam FAQs
Splunk Certification Policy
Candidates registered for a Splunk certification exam must follow the official scheduling and cancellation guidelines to avoid penalties. To reschedule or cancel an exam, you must contact Pearson VUE directly or manage your appointment through your Pearson VUE online account at least 48 hours before the scheduled exam time.
Requests made within 48 hours of the appointment are not permitted, and exams cannot be rescheduled or canceled during this period. If a candidate fails to appear for the exam or does not complete the rescheduling or cancellation process within the allowed timeframe, the exam fee will be forfeited.
As an additional policy, candidates are expected to ensure that all personal details, exam selection, and testing conditions are accurate at the time of booking. Any errors or discrepancies not corrected before the 48-hour cutoff may result in loss of fees and require a new exam registration.
Recertification Policy
All Splunk certifications are valid for three years, starting from the date you pass your highest-level certification exam. It is the candidate’s responsibility to track certification expiration dates. If you do not recertify by the end of the three-year period, you will receive a 90-day grace period to complete the recertification process.
If recertification is not completed within this grace period, your certifications will become inactive, and you will need to restart the certification path. To help avoid this, candidates receive three reminder emails during the final year of the recertification cycle, sent to the last email address on record.
Splunk Certified Cybersecurity Defense Engineer Exam Study Guide
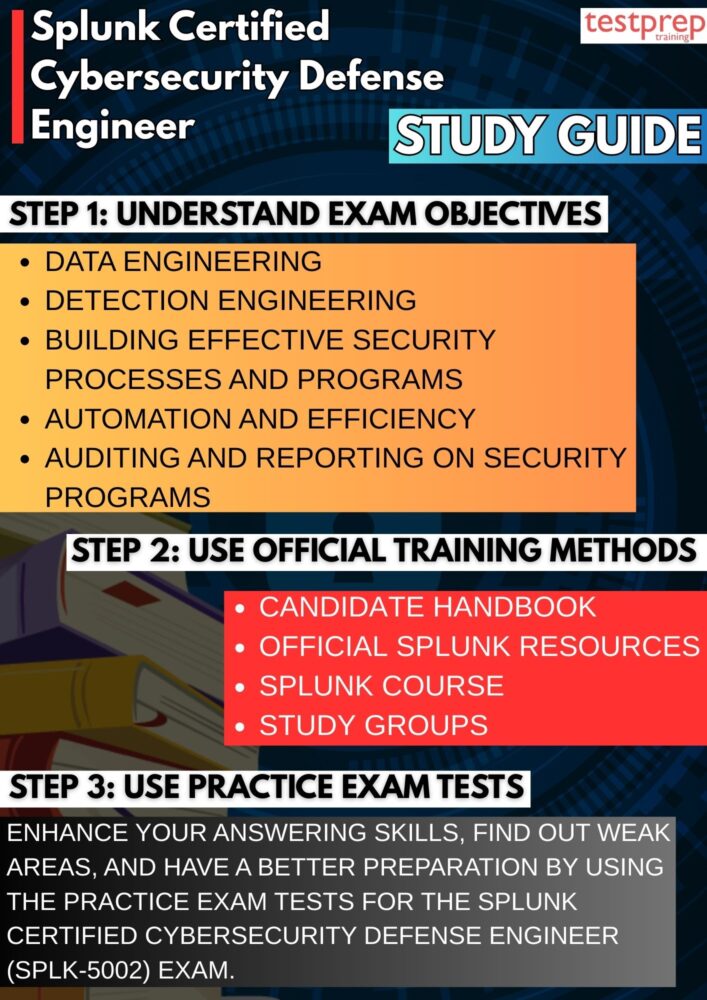
1. Conduct a Capability-Based Review of Exam Objectives
Begin by breaking down the official exam objectives into core defense engineering competencies rather than isolated topics. Analyze how each objective maps to real SOC engineering responsibilities such as detection lifecycle management, alert fidelity improvement, risk-based prioritization, and response optimization. Pay close attention to how Splunk expects detections to evolve—from initial creation to continuous tuning—based on threat intelligence, false-positive analysis, and operational feedback. This approach ensures you prepare at an engineering and design level, not just at a feature-awareness level.
2. Master Exam Expectations Through the Splunk Certification Candidate Handbook
The Splunk Certification Candidate Handbook provides critical insight into how the exam is structured and evaluated. Beyond administrative rules, it helps candidates understand how scenario-based multiple-choice questions are framed, how “best practice” answers are prioritized, and how Splunk evaluates applied judgment over rote knowledge. Reviewing this handbook early allows you to plan your time management strategy, understand retake policies, and align your answers with Splunk’s recommended security and SOC maturity models.
3. Develop Architectural Understanding Using Official Splunk Resources
Deep technical alignment with Splunk guidance is essential.
- Splunk Docs should be studied to understand underlying mechanics such as data models, Common Information Model (CIM) alignment, correlation searches, notable events, risk objects, and SOAR integrations.
- Splunk Blogs offer architectural perspectives, deployment patterns, and real-world lessons from security teams implementing Splunk at scale.
- The Splunk How-To YouTube Channel complements written documentation by demonstrating workflows such as detection tuning, investigation pipelines, and automation use cases.
Focus on understanding design decisions, trade-offs, and scalability considerations rather than only following step-by-step instructions.
4. Apply Threat-Centric Thinking Through Research and Community Challenges
Defense engineers must design detections around adversary behavior, not isolated indicators. Study detection methodologies and attack analyses published by the Splunk Threat Research Team (STRT) to learn how real-world threats are translated into high-confidence detections. Additionally, review investigations and solutions from the Boss of the SOC (BOTS) blog to strengthen your investigative mindset, correlation techniques, and hypothesis-driven analysis. Wherever possible, correlate these insights with your own Splunk usage to reinforce learning through experience.
5. Follow the Splunk Course Catalog as a Progressive Engineering Path
The Splunk course catalog should be approached as a layered learning framework. Foundational courses reinforce core Splunk concepts such as searching, data normalization, and field extraction, while advanced courses focus on enterprise security content, detection logic, and automation workflows. Completing courses in the recommended order helps ensure conceptual continuity and prepares you to understand how ingestion, detection, investigation, and response function together within a resilient SOC architecture.
6. Strengthen Practical Insight Through Study Groups and Communities
Active participation in Splunk and cybersecurity study groups provides exposure to real-world implementation challenges that often surface in exam scenarios. Community discussions frequently highlight detection tuning strategies, SOAR playbook design considerations, and operational pitfalls encountered in production SOCs. These shared experiences help you refine judgment-based decision-making, which is a critical skill assessed at the professional certification level.
7. Use Practice Exams for Engineering-Level Self-Assessment
Practice tests should be treated as diagnostic tools rather than memorization exercises. Analyze each question to understand why one solution is more operationally sound, scalable, or secure than others. Pay special attention to scenarios involving alert prioritization, automation thresholds, and balancing human analysis with orchestration. Reviewing mistakes in detail allows you to close knowledge gaps and sharpen your reasoning under exam time constraints.