ISTQB Certified Tester Security Tester (CT-SEC)

The ISTQB® Security Tester (CT-SEC) certification is an advanced-level qualification designed to equip professionals with the knowledge and skills required to plan, execute, and evaluate security testing activities effectively. This certification emphasizes a multi-dimensional approach to security testing, covering areas such as risk analysis, requirements validation, vulnerability assessment, and human factors. It also provides a strong foundation in the use of security testing tools and international standards.
This certification is a valuable credential for professionals looking to advance their careers in security testing and quality assurance. It not only strengthens technical expertise but also enhances strategic thinking by integrating risk management, security principles, and testing methodologies. By earning this certification, professionals position themselves as capable contributors to building secure, reliable, and resilient software systems in an increasingly threat-driven digital landscape.
Target Audience
The CT-SEC certification is intended for professionals who already possess foundational knowledge in software testing and have some exposure to security testing. It is particularly suitable for:
- Testers aiming to specialize in security testing
- Quality assurance professionals working on security-sensitive applications
- Security analysts and consultants seeking structured certification
- Test managers and engineers involved in risk-based testing strategies
Eligibility Criteria
To pursue the CT-SEC certification, candidates must meet the following requirements:
- Hold the ISTQB® Certified Tester Foundation Level (CTFL) certification
- Have a minimum of three years of relevant experience in academic, professional, or consulting roles related to testing or security
It is recommended to verify specific eligibility requirements with your local ISTQB® Member Board or accredited exam provider, as criteria may vary slightly by region.
Key Business Outcomes
Professionals who successfully achieve the CT-SEC certification are expected to demonstrate advanced capabilities in security testing. The certification enables candidates to:
- Comprehensive Security Test Planning
- Design and execute security tests based on multiple perspectives, including:
- Policy-based
- Risk-based
- Standards-based
- Requirements-based
- Vulnerability-based
- Design and execute security tests based on multiple perspectives, including:
- Integration with Development Lifecycle
- Align security testing activities with different stages of the software development lifecycle (SDLC) to ensure continuous security validation.
- Risk Assessment and Threat Analysis
- Apply risk assessment techniques to:
- Identify potential security threats
- Evaluate their severity and impact
- Anticipate future vulnerabilities
- Apply risk assessment techniques to:
- Security Test Evaluation and Improvement
- Assess existing security test suites and identify:
- Gaps in coverage
- Opportunities for improvement
- Additional test scenarios
- Assess existing security test suites and identify:
- Policy and Procedure Analysis
- Evaluate organizational security policies and testing outcomes to determine their effectiveness and compliance.
- Security Test Design
- Define clear security testing objectives based on:
- System functionality
- Technological architecture
- Known vulnerabilities
- Define clear security testing objectives based on:
- Selection of Testing Approaches
- Analyze different scenarios and determine the most appropriate security testing techniques and methodologies.
- Enhancement of Security Coverage
- Identify areas where additional or more advanced testing is required to strengthen system security.
- Evaluation of Security Mechanisms
- Assess the effectiveness of implemented security controls and mechanisms within applications.
- Security Awareness Contribution
- Support organizations in building a culture of information security awareness among teams and stakeholders.
- Attacker Mindset Application
- Adopt an ethical attacker perspective to:
- Gather critical system information
- Simulate real-world attack scenarios in controlled environments
- Understand methods used to conceal attack traces
- Adopt an ethical attacker perspective to:
- Reporting and Communication
- Evaluate and improve security test reports to ensure:
- Accuracy
- Clarity
- Relevance for stakeholders
- Evaluate and improve security test reports to ensure:
- Tool Selection and Utilization
- Identify security testing needs and:
- Map them to appropriate tools
- Evaluate and select suitable tools based on project requirements
- Identify security testing needs and:
- Standards and Best Practices
- Understand the value of security testing standards, and know where to access and apply them effectively.
Exam Details
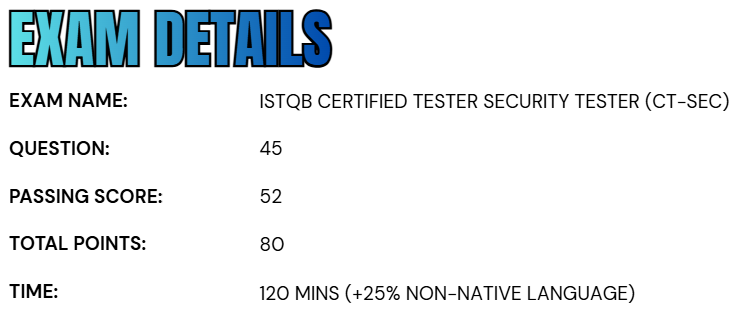
- The ISTQB® Certified Tester – Security Tester (CT-SEC) examination is structured to comprehensively evaluate a candidate’s expertise in security testing concepts and practices.
- The exam consists of 45 questions, with a total of 80 marks available.
- To successfully pass, candidates are required to achieve a minimum score of 52 marks, demonstrating a solid understanding of the subject matter.
- The standard duration of the examination is 120 minutes; however, candidates who are taking the exam in a non-native language are granted an additional 25% time allowance to ensure fairness and accessibility.
Course Outline
The ISTQB Certified Tester Security Tester (CT-SEC) exam covers the following topics:
1. Understand The Basis of Security Testing – 105 mins.
1.1 Security Risks
- (K2) Understand the role of risk assessment in supplying information for security test planning and design and aligning security testing with business needs
- (K4) Identify the significant assets to be protected, the value of each asset and the data required to assess the level of security needed for each asset
- (K4) Analyze the effective use of risk assessment techniques in a given situation to identify current and future security threats
1.2 Information Security Policies and Procedures
- (K2) Understand the concept of security policies and procedures and how they are applied in information systems
- (K4) Analyze a given set of security policies and procedures along with security test results to determine effectiveness
1.3 Security Auditing and Its Role in Security Testing
- (K2) Understand the purpose of a security audit
2. Learn Security Testing Purposes, Goals and Strategies – 130 mins.
2.1 Introduction
2.2 The Purpose of Security Testing
- (K2) Understand why security testing is needed in an organization, including benefits to the organization such as risk reduction and higher levels of confidence and trust
2.3 The Organizational Context
- (K2) Understand how project realities, business constraints, software development lifecycle, and other considerations affect the mission of the security testing team
2.4 Security Testing Objectives
- (K2) Explain why security testing goals and objectives must align with the organization’s security policy and other test objectives in the organization
- (K3) For a given project scenario, demonstrate the ability to identify security test objectives based on functionality, technology attributes and known vulnerabilities
- (K2) Understand the relationship between information assurance and security testing
2.5 The Scope and Coverage of Security Testing Objectives
- (K3) For a given project, demonstrate the ability to define the relationship between security test objectives and the need for strength of integrity of sensitive digital and physical assets
2.6 Security Testing Approaches
- (K4) Analyze a given situation and determine which security testing approaches are most likely to succeed
- (K4) Analyze a situation in which a given security testing approach failed, identifying the likely causes of failure
- (K3) For a given scenario, demonstrate the ability to identify the various stakeholders and illustrate the benefits of security testing for each stakeholder group
2.7 Improving the Security Testing Practices
- (K4) Analyze KPIs (key performance indicators) to identify security testing practices needing improvement and elements not needing improvement
3. Understand Security Testing Processes – 140 mins.
3.1 Security Test Process Definition
- (K3) For a given project, demonstrate the ability to define the elements of an effective security test process
3.2 Security Test Planning
- (K4) Analyze a given security test plan, giving feedback on strengths and weaknesses of the plan
3.3 Security Test Design
- (K3) For a given project, implement conceptual (abstract) security tests, based on a given security test approach, along with identified functional and structural security risks
- (K3) Implement test cases to validate security policies and procedures
3.4 Security Test Execution
- (K2) Understand the key elements and characteristics of an effective security test environment
- (K2) Understand the importance of planning and obtaining approvals before performing any security test
3.5 Security Test Evaluation
- (K4) Analyze security test results to determine the following:
- Nature of security vulnerability
- Extent of security vulnerability
- Potential impact of security vulnerability
- Suggested remediation
- Optimal test reporting methods
3.6 Security Test Maintenance
- (K2) Understand the importance of maintaining security testing processes given the evolving nature of technology and threats
4. Learn about Security Testing Throughout the Software Lifecycle – 225 mins.
4.1 Role of Security Testing in a Software Lifecycle
- (K2) Explain why security is best achieved within a lifecycle process
- (K3) Implement the appropriate security-related activities for a given software lifecycle (e.g., iterative, sequential)
4.2 The Role of Security Testing in Requirements
- (K4) Analyze a given set of requirements from the security perspective to identify deficiencies
4.3 The Role of Security Testing in Design
- (K4) Analyze a given design document from the security perspective to identify deficiencies
4.4 The Role of Security Testing in Implementation Activities
- (K2) Understand the role of security testing during component testing
- (K3) Implement component level security tests (abstract) given a defined coding specification
- (K4) Analyze the results from a given component level test to determine the adequacy of code from the security perspective
- (K2) Understand the role of security testing during component integration testing
- (K3) Implement component integration security tests (abstract) given a defined system specification
4.5 The Role of Security Testing in System and Acceptance Test Activities
- (K3) Implement an end-to-end test scenario for security testing which verifies one or more given security requirements and tests a described functional process
- (K3) Demonstrate the ability to define a set of acceptance criteria for the security aspects of a given acceptance test
4.6 The Role of Security Testing in Maintenance
- (K3) Implement an end-to-end security retest/regression test approach based on a given scenario
5. Learn About Testing Security Mechanisms – 240 mins.
5.1 System Hardening
- (K2) Understand the concept of system hardening and its role in enhancing security
- (K3) Demonstrate how to test the effectiveness of common system hardening mechanisms
5.2 Authentication and Authorization
- (K2) Understand the relationship between authentication and authorization and how they are applied in securing information systems
- (K3) Demonstrate how to test the effectiveness of common authentication and authorization mechanisms
5.3 Encryption
- (K2) Understand the concept of encryption and how it is applied in securing information systems
- (K3) Demonstrate how to test the effectiveness of common encryption mechanisms
5.4 Firewalls and Network Zones
- (K2) Understand the concept of firewalls and the use of network zones and how they are applied in securing information systems
- (K3) Demonstrate how to test the effectiveness of existing firewall implementations and network zones
5.5 Intrusion Detection
- (K2) Understand the concept of intrusion detection tools and how they are applied in securing information systems
- (K3) Demonstrate how to test the effectiveness of existing intrusion detection tool implementations
5.6 Malware Scanning
- (K2) Understand the concept of malware scanning tools and how they are applied in securing information systems
- (K3) Demonstrate how to test the effectiveness of existing malware scanning tool implementations
5.7 Data Obfuscation
- (K2) Understand the concept of data obfuscation tools and how they are applied in securing information systems
- (K3) Demonstrate how to test the effectiveness of data obfuscation approaches
6. Concept of Human Factors in Security Testing – 105 mins.
6.1 Understanding the Attackers
- (K2) Explain how human behavior can lead to security risks and how it impacts the effectiveness of security testing
- (K3) For a given scenario, demonstrate the ability to identify ways in which an attacker could discover key information about a target and apply measures to protect the environment
- (K2) Explain the common motivations and sources for performing computer system attacks
- (K4) Analyze an attack scenario (attack performed and discovered) and identify possible sources and motivation for the attack
6.2 Social Engineering
- (K2) Explain how security defenses can be compromised by social engineering
6.3 Security Awareness
- (K2) Understand the importance of security awareness throughout the organization
- (K3) Given certain test outcomes, apply appropriate actions to increase security awareness
7. Understand Security Test Evaluation and Reporting – 70 mins.
7.1 Security Test Evaluation
- (K2) Understand the need to revise security expectations and acceptance criteria as the scope and goals of a project evolve
7.2 Security Test Reporting
- (K2) Understand the importance of keeping security test results confidential and secure
- (K2) Understand the need to create proper controls and data-gathering mechanisms to provide the source data for the security test status reports in a timely, accurate, and precise fashion (e.g., a security test dashboard)
- (K4) Analyze a given interim security test status report to determine the level of accuracy, understandability, and stakeholder appropriateness
8. Explore Security Testing Tools – 55 mins
8.1 Types and Purposes of Security Testing Tools
- (K2) Explain the role of static and dynamic analysis tools in security testing
8.2 Tool Selection
- (K4) Analyze and document security testing needs to be addressed by one or more tools
- (K2) Understand the issues with open source tools
- (K2) Understand the need to evaluate the vendor’s capabilities to update tools on a frequent basis to stay current with security threats
9. Learn Standards and Industry Trends – 40 mins.
9.1 Understanding Security Testing Standards
- (K2) Understand the benefits of using security testing standards and where to find them
- (K2) Understand the difference in applicability of standards in regulatory versus contractual situations
9.2 Applying Security Standards
- (K2) Understand the difference between mandatory (normative) and optional (informative) clauses within any standard
9.3 Industry Trends
- (K2) Understand where to learn of industry trends in information security
ISTQB Certified Tester Security Tester (CT-SEC) Exam FAQs
ISTQB Certified Tester Security Tester (CT-SEC) Exam Study Guide
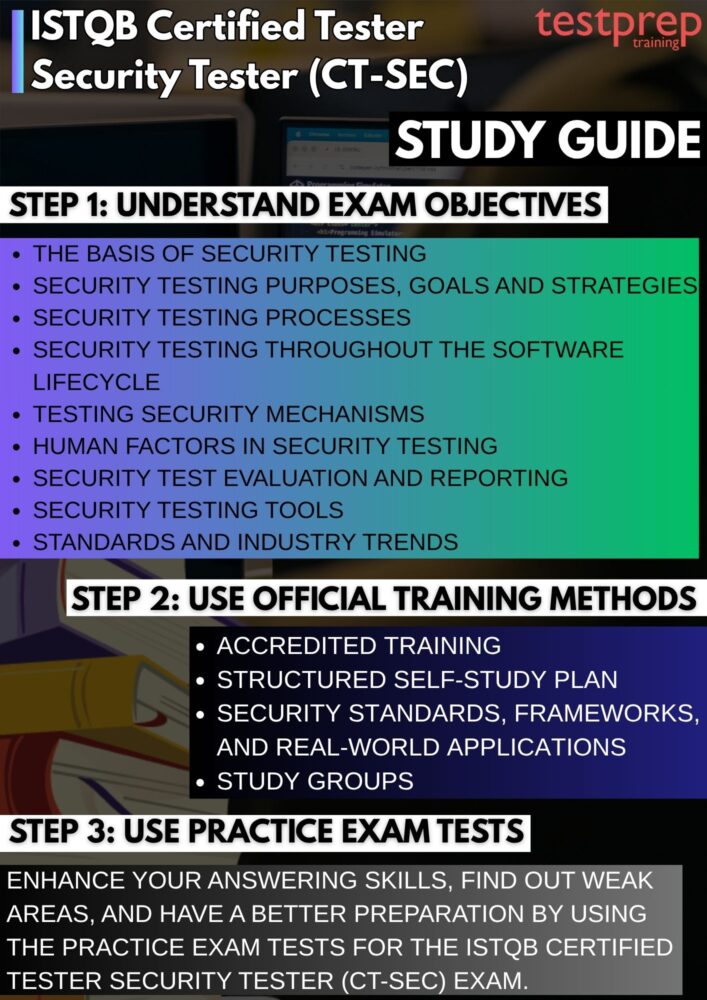
1. Develop a Deep Understanding of the Exam Structure and Syllabus
Start your preparation by carefully analyzing the official CT-SEC syllabus and exam objectives. Break down each module and identify the learning objectives, cognitive levels (K-levels), and expected outcomes. Pay special attention to areas such as risk-based security testing, vulnerability identification, security standards, test design techniques, and human-related security risks. Understanding not just what topics are covered, but also how deeply you are expected to know them, will help you allocate time effectively and avoid over- or under-preparation. Create a study roadmap that maps syllabus sections to a realistic timeline.
2. Enroll in ISTQB® Accredited Training for Structured Learning
While self-study is important, enrolling in training from ISTQB®-accredited providers can significantly enhance your preparation. These programs are validated by ISTQB® Member Boards, ensuring alignment with the official syllabus and exam expectations. Accredited training typically includes expert-led sessions, real-world examples, case studies, and interactive discussions, which help bridge the gap between theory and practical application. Additionally, such courses often provide exam-oriented materials, practice questions, and revision sessions, giving you a more structured and guided learning experience.
3. Strengthen Conceptual Clarity Through Focused Self-Study
Self-study plays a critical role in mastering CT-SEC concepts. Use the official syllabus as your primary reference and supplement it with recommended textbooks, technical documentation, and trusted online resources. Focus on building a clear understanding of core principles, such as threat modeling, risk assessment techniques, security test planning, and vulnerability analysis, rather than rote memorization. Make detailed notes, summarize key points, and revisit complex topics multiple times to ensure long-term retention.
4. Explore Security Standards, Frameworks, and Real-World Applications
To deepen your expertise, study widely recognized security standards and frameworks such as OWASP Top 10, ISO/IEC 27001, and common security testing methodologies. Understanding these frameworks will help you relate theoretical knowledge to real-world security challenges. Try to analyze practical scenarios, case studies, and incident reports to see how security vulnerabilities are identified and mitigated in actual projects. This approach not only improves comprehension but also prepares you for scenario-based questions commonly found in advanced-level exams.
5. Engage with Study Groups and Professional Communities
Joining study groups, discussion forums, or professional communities can greatly enhance your preparation. Platforms such as online forums, LinkedIn groups, or local testing communities allow you to exchange knowledge, clarify doubts, and discuss complex topics with peers and industry professionals. Collaborative learning often exposes you to different perspectives and problem-solving approaches, which can be especially useful for understanding nuanced security concepts. Teaching or explaining topics to others is also an effective way to reinforce your own understanding.
6. Practice Extensively with Mock Exams and Scenario-Based Questions
Consistent practice is essential for exam success. Attempt multiple mock tests, sample papers, and scenario-based questions to become familiar with the exam pattern, question style, and time constraints. Focus on understanding why an answer is correct or incorrect, rather than just selecting the right option. Track your performance to identify weak areas and adjust your study plan accordingly. Practicing under timed conditions will also help you improve speed, accuracy, and confidence.
7. Perform Thorough Revision and Exam Readiness Assessment
As the exam approaches, dedicate time to structured revision. Consolidate your notes into quick-reference summaries, mind maps, or flashcards for efficient review. Revisit challenging topics, key definitions, and important frameworks to ensure clarity. In this phase, focus on refining your understanding, eliminating confusion, and strengthening weak areas identified during practice tests. Additionally, simulate full-length exams to assess your readiness and ensure you can manage time effectively during the actual test.