Software delivery has evolved into a continuous, high-velocity process where applications are deployed and updated faster than ever before. Organizations now rely on automated pipelines, distributed teams, and open-source ecosystems to stay competitive. While this transformation has improved speed and scalability, it has also fundamentally changed the security landscape. Application vulnerabilities are no longer isolated technical flaws; they represent direct business risks. For candidates preparing for the GitHub Advanced Security Certification (GH-500), understanding this shift is essential, as the certification is grounded in modern, workflow-driven application security practices rather than traditional, siloed security models.
Why Application Security has become a Core DevOps Skill?
In earlier development models, security issues were often discovered during final testing or after deployment. This approach aligned with slower release cycles but is incompatible with modern DevOps practices. Today, applications are updated frequently, dependencies change continuously, and infrastructure is defined as code. Under these conditions, vulnerabilities can be introduced at any stage of development and can propagate quickly across environments.
As a result, application security has shifted from a periodic activity to a continuous responsibility. DevOps teams must be able to identify insecure code patterns, vulnerable dependencies, and configuration risks as part of their everyday work. Security is no longer a separate phase—it is embedded into how software is designed, built, and maintained.
From Security Gates to Continuous Assurance
- Traditional security models relied heavily on manual reviews and late-stage approvals. While thorough, these practices often slowed delivery and created friction between development and security teams. Modern DevOps environments require a different approach: one that provides ongoing assurance without disrupting velocity.
- This has led to the adoption of automated, developer-friendly security controls that operate directly within version control systems and CI/CD pipelines. Instead of blocking progress at the end, security checks run continuously, providing early visibility into risks and enabling teams to address issues when they are easiest and least costly to fix.
DevSecOps and Shared Ownership of Security
- The integration of security into DevOps workflows has formalized into what is commonly known as DevSecOps. In this model, security is treated as a shared responsibility rather than a centralized function. Developers, operations engineers, and security professionals collaborate using common tools and processes, supported by automation and policy-driven controls.
- For DevOps practitioners, this means security awareness is now a core competency. Teams are expected to understand the implications of security findings, evaluate their impact, and apply remediation strategies that align with both technical and business priorities.
Application Security as a Developer-Centric Discipline
- Modern applications depend heavily on third-party libraries and shared codebases. Vulnerabilities are frequently introduced through dependencies or mismanaged secrets rather than custom logic alone. Because these risks surface during development, developers and DevOps engineers are often the first to encounter them.
- This reality has made application security a practical, hands-on discipline. It requires the ability to interpret scan results, distinguish high-risk issues from low-impact findings, and respond appropriately within active development workflows. These skills are now expected of professionals working in DevOps and platform engineering roles.
Relevance to GitHub Advanced Security and GH-500
- GitHub Advanced Security is designed around this modern security paradigm. By embedding code scanning, dependency analysis, and secret detection directly into GitHub repositories and workflows, it enables security to operate where development happens. This approach aligns closely with DevSecOps principles and reflects how organizations manage application risk at scale.
- The GH-500 certification builds on this foundation. It evaluates a candidate’s ability to apply application security concepts within GitHub-based development environments, emphasizing practical judgment over theoretical knowledge. Understanding why application security has become a core DevOps skill provides the necessary context for the topics and scenarios explored throughout the exam and the broader preparation guide.
Understanding GitHub Advanced Security (GHAS) as a Platform
GitHub Advanced Security is designed around a simple but powerful idea: application security is most effective when it runs where developers already work.
Security Built Into the Developer Workflow
- Instead of treating security as a separate system that analyzes code after the fact, GHAS embeds security checks directly into repositories, pull requests, and automated workflows. This tight integration ensures that security signals appear at the same moment developers are making decisions about code changes.
- By operating natively within GitHub, GHAS reduces friction between development and security objectives. Developers do not need to learn entirely new tools or leave their workflow to address risks. Security becomes a continuous, visible part of the development process rather than a disruptive checkpoint introduced late in the lifecycle.
A Unified View of Application Risk
- One of the defining strengths of GHAS as a platform is its ability to consolidate multiple dimensions of application security into a single environment. Modern applications are exposed to risk through custom code, open-source dependencies, and operational oversights such as exposed secrets. GHAS approaches these risks holistically by providing capabilities that address each layer within the same platform.
- Rather than generating isolated reports, GHAS presents findings in context—linked to specific repositories, commits, and pull requests. This contextualization allows teams to understand not only what the issue is, but where it originated and how it impacts the application, making remediation more precise and efficient.
Code Intelligence Through Advanced Analysis
- At the code level, GHAS enables deep security analysis that goes beyond simple pattern matching. Its scanning capabilities analyze how code behaves, how data flows through an application, and how different components interact. This approach helps uncover complex vulnerabilities that might otherwise remain hidden, especially in large or mature codebases.
- From a platform perspective, this intelligence is tightly coupled with version control. Security findings are tracked alongside code changes, enabling teams to see when vulnerabilities were introduced and how fixes evolve over time. This alignment between code history and security insights is critical for maintaining long-term application integrity.
Managing Dependency and Supply Chain Risk
- Modern software development is inseparable from open-source usage, which introduces supply chain considerations into everyday development work. GHAS treats dependency security as a first-class concern by continuously monitoring third-party components used within repositories. When vulnerabilities are identified, they are surfaced directly within GitHub, often alongside recommended remediation actions.
- This capability shifts dependency management from a reactive cleanup task to a proactive security practice. Teams can evaluate the risk of introducing or updating dependencies during code review, rather than discovering issues after deployment. As a platform feature, this integration reinforces the idea that secure dependency management is part of normal development responsibility.
Preventing and Responding to Secret Exposure
- Credential exposure remains one of the most common and damaging application security issues. GHAS addresses this risk by actively identifying secrets within repositories and, where configured, preventing them from being committed in the first place. This preventive approach reflects a platform-level commitment to reducing high-impact security incidents before they occur.
- When secrets are detected, alerts are tied directly to the relevant code and repository context. This enables rapid response and remediation while maintaining clear accountability within development teams.
Platform-Level Visibility and Governance
- Beyond individual repositories, GHAS provides organizational visibility into application security posture. Security teams and platform administrators can assess trends, identify high-risk areas, and evaluate the effectiveness of remediation efforts across projects. This centralized visibility supports governance without removing autonomy from development teams.
- From an exam preparation standpoint, this reinforces an important theme of GH-500: GHAS is not just a scanning tool, but a security management platform that supports both tactical remediation and strategic oversight.
Why This Perspective Matters for GH-500 Candidates
- The GH-500 certification is built around understanding how GitHub Advanced Security functions as part of real development environments. Candidates are expected to recognize how security signals flow through GitHub, how different features complement one another, and how security decisions are made within active workflows.
- Viewing GHAS as an integrated platform—rather than a collection of independent tools—helps candidates approach the exam with the right mindset. It prepares them to reason through scenarios where security, development velocity, and operational constraints intersect, which is central to how GitHub Advanced Security is used in practice.
What Is the GitHub Advanced Security Certification (GH-500)?
The GitHub Advanced Security Certification (GH-500) is a role-focused professional certification designed to validate a candidate’s ability to apply application security practices directly within GitHub-based development environments. Rather than testing abstract security theory or isolated tooling knowledge, GH-500 evaluates how well a professional can use GitHub Advanced Security (GHAS) to identify, manage, and remediate security risks across real software projects.
This certification reflects how modern organizations approach application security today—by embedding it into developer workflows instead of treating it as a separate or downstream activity. GH-500 is positioned for professionals who already work with GitHub and are responsible for securing code, dependencies, and development pipelines at scale.
Purpose and Intent of the GH-500 Certification
The primary goal of GH-500 is to assess practical security capability within the GitHub ecosystem. GitHub Advanced Security is deeply integrated into repositories, pull requests, and CI/CD workflows, and the certification is designed to confirm that candidates understand how these integrations function in real-world scenarios.
Rather than asking candidates to memorize feature lists, the exam emphasizes understanding why and when specific security capabilities are used. This includes interpreting security findings, recognizing the implications of alerts, and applying security controls in a way that supports continuous delivery without compromising risk management. The certification aligns closely with how GitHub Advanced Security is used in enterprise development environments, where security must scale across teams and repositories.
Who should take the GH-500 Certification Exam?
GH-500 is not an entry-level GitHub credential. It is intended for professionals who already have hands-on exposure to GitHub and are involved in securing software during development. This typically includes developers who contribute to secure coding initiatives, DevOps engineers responsible for pipeline security, and security or platform engineers who manage GitHub environments.
Candidates are expected to be comfortable navigating repositories, understanding pull request workflows, and working with automated checks. The certification assumes familiarity with GitHub concepts and focuses instead on how security features are configured, interpreted, and operationalized using GitHub Advanced Security.
What are the Certification Measures in Practice?
The GH-500 exam validates a candidate’s ability to work with GitHub Advanced Security as a cohesive security platform. This includes understanding how different security signals – such as code analysis results, dependency vulnerabilities, and secret exposure alerts—are generated and how they relate to one another within a development lifecycle.
A strong emphasis is placed on security decision-making. Candidates must demonstrate awareness of how security findings affect development velocity, how remediation choices impact risk, and how security controls can be enforced without disrupting collaboration. This makes the certification particularly relevant for roles that operate at the intersection of development, operations, and security.

Alignment With GitHub Advanced Security Capabilities
The GH-500 certification is closely aligned with the capabilities offered by GitHub Advanced Security. Exam objectives are structured around how GHAS features are used to secure repositories, manage organizational security posture, and support DevSecOps practices. This includes understanding how security scans are triggered, how alerts are reviewed and resolved, and how security visibility is maintained across projects.
Because the certification is tied directly to GitHub’s security tooling, it reflects current, platform-driven security practices rather than vendor-neutral theory. This makes GH-500 particularly valuable for professionals working in environments where GitHub is the central collaboration and delivery platform.
Why GH-500 Matters in Modern Development Roles?
As application security becomes a shared responsibility across development teams, organizations increasingly look for professionals who can operate security tools within everyday workflows. GH-500 serves as a validation of this capability. It demonstrates that a candidate can apply security concepts in context—within repositories, pull requests, and automated pipelines—rather than in isolation.
For students and professionals preparing for this exam, understanding GH-500 as a certification of applied, workflow-driven security expertise is critical. It sets the tone for the rest of the preparation journey, which focuses on how GitHub Advanced Security supports secure software delivery in practical, scalable ways.
Exam Structure and Assessment Approach: GitHub Advanced Security (GH-500)
The GitHub Advanced Security Certification (GH-500) is designed to validate not just theoretical knowledge of GitHub security features but a candidate’s ability to apply them effectively within live software development environments. Unlike conventional credential exams that emphasize memorization, GH-500 assesses how you would use GitHub Advanced Security (GHAS) features to support secure workflows, interpret alerts, configure tools, and make context-based decisions in real-world scenarios.
Exam Format and Structure
At its core, the GH-500 exam blends scenario-based reasoning with practical understanding of GHAS capabilities. The intent is to mirror the kinds of decisions security, DevOps, and development professionals make when working with security tooling embedded into GitHub repositories and workflows. Questions focus on interpreting security findings, configuring protection mechanisms, and understanding implications of different security actions—not merely recalling feature names.
Duration and Delivery
Candidates have 100 minutes to complete the assessment—a time frame that balances thoughtful analysis with practical proficiency. This duration accommodates a range of question types that include traditional multiple-choice items, scenario-based prompts, and sometimes interactive elements that reflect practical tasks.
The exam is proctored, ensuring integrity and consistent testing conditions regardless of delivery mode. It is typically administered through approved testing partners like Pearson VUE.
Language Accessibility
To support a global candidate base, GH-500 is offered in multiple languages, including English, Spanish, Portuguese (Brazil), Korean, and Japanese. This multilingual support helps ensure that candidates can demonstrate their skills in the language they are most comfortable with.
Assessment Approach: Beyond Memorization
One of the defining aspects of GH-500’s assessment strategy is its emphasis on contextual understanding and applied judgment rather than simple recall.
Scenario-Driven Questions
The exam places candidates in typical development and security scenarios—for example, interpreting an alert triggered by dependency analysis in a pull request, deciding how to respond to a secret scanning notification, or choosing how to configure a CodeQL scan for optimal early detection of vulnerabilities. These scenarios reflect real decisions practitioners face when integrating security into CI/CD pipelines.
This method of assessment ensures that professionals are prepared not just to recognize features like secret scanning or Dependabot alerts, but to apply them appropriately to enhance code security while maintaining development velocity.
Feature Interplay and Workflow Integration
Rather than isolating features, GH-500 frequently tests understanding of how different parts of GitHub Advanced Security work together. For example:
- How secret scanning interacts with push protection configurations
- How Dependabot alerts relate to dependency review workflows
- How CodeQL analysis results should influence remediation and policy adjustments
This reflects the reality that application security is rarely about single features in isolation—it is about orchestrating multiple capabilities in a cohesive, efficient way within development practices.
Practical Skills Emphasized by the Assessment
The GH-500 exam measures competencies that professionals regularly exercise in secure DevOps environments. These include:
- Interpreting security output: Recognizing which alerts require prioritized action versus informational context
- Configuring protective mechanisms: Setting up and tuning tools like secret scanning or CodeQL to support specific project needs
- Balancing security and delivery: Deciding when security checks should be enforced without disrupting developer productivity
These skills align with how organizations operationalize security within GitHub—security must be effective, actionable, and integrated into existing workflows rather than siloed or disruptive.
Why This Matters for Preparation
Understanding the exam structure is more than logistical—it shapes how candidates should prepare. Because GH-500 emphasizes practical application and real-world scenario interpretation, preparation strategies should move beyond memorization. Focus on hands-on experience with GHAS features, interpreting outputs from scans and alerts, and simulating decision-based scenarios that mirror what you might encounter in the exam and in day-to-day work.
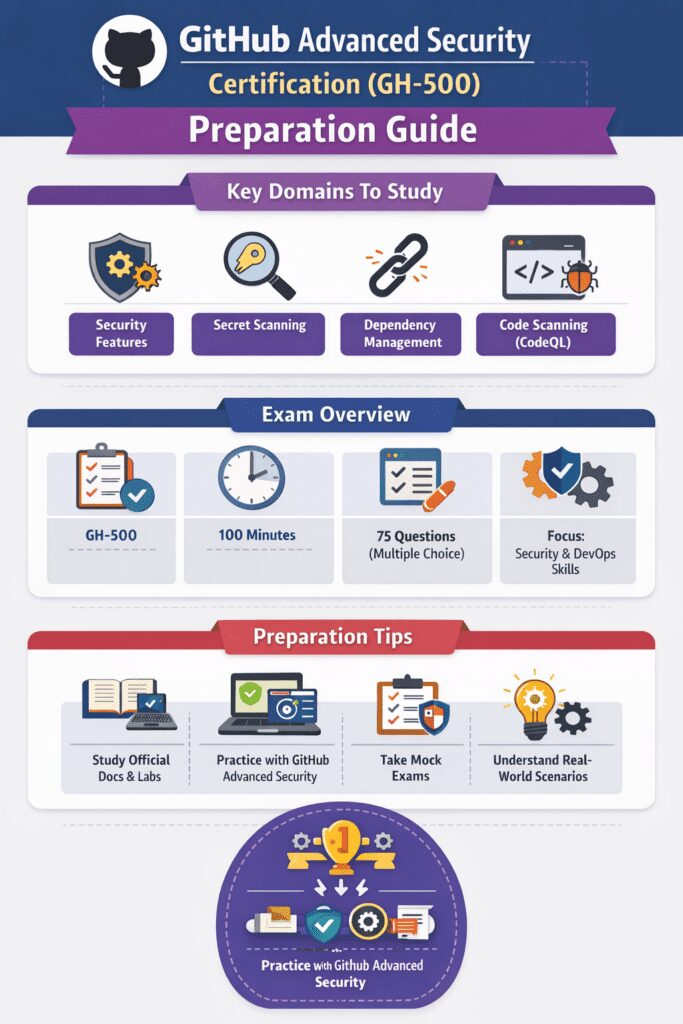
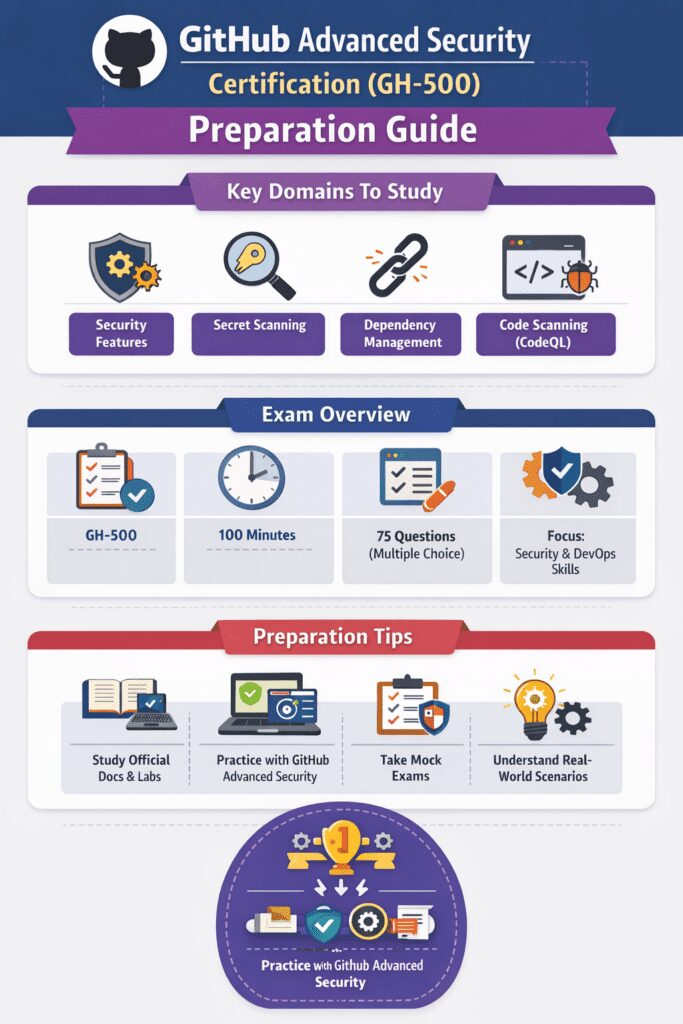
Core Security Exam Domains Covered in the GH-500 Exam
The GitHub Advanced Security Certification (GH-500) evaluates candidates on a set of core security domains that reflect the real-world application of GitHub Advanced Security (GHAS) features within software development lifecycles. Rather than isolating theoretical concepts, each domain represents foundational competencies you must demonstrate in operational contexts—whether interpreting scan results, configuring security controls, or applying remediation practices that balance both security and development workflow needs.
This section provides an in-depth look at the major content areas tested by the exam, emphasizing both what you need to know and how each domain connects to everyday secure development responsibilities.
1. Describe GHAS Security Features and Functionality
- At its core, GitHub Advanced Security integrates powerful security capabilities directly into the GitHub platform, enabling teams to find and fix vulnerabilities within repositories and workflows. The GH-500 exam assesses your understanding of these features—what they do, why they matter, and how they support secure development.
- Candidates must be familiar with the purpose and interplay of key GHAS tools, including code scanning, dependency review, secret scanning, and associated dashboards that surface risks and insights across projects. This domain captures the conceptual foundation that enables informed decisions about security enforcement, prioritization of risks, and integration of security into CI/CD pipelines.
- Understanding this domain ensures you can articulate how each capability contributes to the detection and mitigation of software vulnerabilities, and how GHAS as a platform supports a proactive, developer-centric security posture.
2. Configure and Use Secret Scanning
- Secrets such as API keys, tokens, and certificates are highly sensitive and, if exposed, can quickly lead to credential compromise and unauthorized access. GHAS’s secret scanning capability continuously monitors repository contents and commit history to detect patterns that resemble sensitive data.
- The GH-500 exam tests your ability to configure secret scanning for an organization and interpret alerts when potential exposures are detected. Candidates should understand the mechanics of scanning, how push protection can be enabled to prevent secrets from being committed, and how to manage responses when secret leaks are identified.
- This domain reflects a real-world need: preventing credential exposure reduces security incidents and protects critical infrastructure components. The exam evaluates not only your knowledge of how secret scanning operates, but also your ability to apply it as part of a secure development lifecycle.
3. Configure and Use Dependency Management
- Modern applications rely extensively on third-party libraries and open-source components, which introduces supply chain security considerations that extend far beyond original application code. GHAS provides tools that help teams assess the security impact of dependencies and manage known vulnerabilities.
- This domain focuses on your ability to use dependency review features and interpret alerts related to vulnerable packages. Candidates should understand when and how GitHub surfaces alerts for known vulnerabilities (often powered by Dependabot) and how to use that information to make informed decisions during code review and merge processes.
- Configuration tasks may involve enabling alerts at the appropriate scope, tailoring management of dependency updates, and communicating risk with development teams to ensure vulnerabilities are addressed promptly and appropriately.
- The GH-500 exam places significant emphasis on this domain because dependency and supply chain vulnerabilities are among the most common threats in contemporary software systems, and effective management helps prevent high-impact security incidents.


4. Configure and Use Code Scanning with CodeQL
- One of the most technically robust components of GitHub Advanced Security is code scanning powered by CodeQL. CodeQL performs semantic analysis of source code to identify patterns that may indicate security weaknesses. Rather than simple pattern matching, CodeQL understands how data and control flow through an application, enabling deeper detection of both common and complex vulnerabilities.
- In this domain, the GH-500 exam tests your ability to configure and manage code scanning workflows, interpret scan results, and prioritize remediation activities based on context and severity. You should understand how to integrate CodeQL scanning into GitHub Actions workflows, tune rules or queries to reduce false positives, and interpret findings in a way that informs effective remediation.
- Because code scanning often produces detailed results across large codebases, the ability to interpret and take action on scan outputs is a key professional skill. GH-500 evaluates not simply whether you can run a scan, but whether you can use the results intelligently to support secure code quality decisions.
5. Describe GHAS Best Practices, Results, and Remediation
- The final core domain addresses how to interpret and act upon security outputs generated by GHAS tools. In practice, generating alerts or analysis results is only valuable if development teams can understand and respond to them appropriately.
- This domain measures your understanding of how findings are categorized, how severity and risk impact remediation prioritization, and how teams can integrate response workflows into development cycles. It also evaluates your awareness of best practices—how security signals should inform coding, review, and deployment decisions—and how organizational policies or settings influence these practices.
- Candidates should be prepared to analyze scenarios where multiple vulnerabilities or alerts are present, articulate remediation strategies that align with project priorities, and understand how to support collaboration between developers, DevOps engineers, and security teams.
Real-World Skills Evaluated for the GH-500 Exam
While the GitHub Advanced Security Certification (GH-500) exam is structured around concrete domains such as code scanning, dependency management, and secret detection, its design inherently evaluates a broader set of professional capabilities that extend beyond tool usage. These “indirect” skills reflect how security practices are executed in live development environments—skills that are essential for professionals working at the intersection of development, operations, and security. Recognizing these underlying competencies can significantly improve how candidates prepare for the exam and apply their knowledge in real-world settings.
Contextual Interpretation of Security Findings
One of the most valuable skills implicitly assessed by GH-500 is the ability to interpret security output within context. GitHub Advanced Security generates a variety of signals—alerts from code scanning, vulnerability notifications from dependency analysis, and secret exposure warnings. However, alerts alone are not sufficient; professionals must understand what these signals mean for their specific project, how critical a finding is, and what steps are appropriate for remediation.
For example, a code scanning result may highlight a potential vulnerability, but interpreting its severity requires understanding the application’s architecture, the function’s role, and how the finding might impact runtime behavior. Likewise, a dependency alert could be low risk or high risk depending on how the library is used. The exam tests this through scenario-based questions that ask candidates to reason about findings—not just recognize them.
This contextual interpretation skill is crucial in real development teams, where security practitioners must sift through noise and focus on meaningful risks that genuinely affect application integrity and business outcomes.
Applied Decision-Making in Development Workflows
Because GH-500 is designed to mirror real workflows, it indirectly assesses candidates’ capacity for applied decision-making. In a live environment, security decisions rarely have a single correct answer. Teams must often balance the urgency of a release with the need to address a vulnerability, decide when to block merges versus when to document mitigations, and collaborate with stakeholders across functions to prioritize actions.
The exam’s scenario-based questions require candidates to choose options that reflect thoughtful decision-making rather than rote recollection. This includes understanding how features such as push protection, dependency alerts, and security policies impact development velocity and team collaboration.
These decision contexts replicate professional situations where developers, DevOps engineers, and security leads must negotiate priorities that align secure practices with delivery timelines—an increasingly important skill as organizations adopt continuous delivery and DevSecOps practices.
Integration of Security Into Standard Development Practices
Another real-world skill GH-500 indirectly evaluates is the ability to integrate security into everyday development activities. In practice, security cannot be siloed; it must coexist with coding, testing, pull requests, and deployment processes. GitHub Advanced Security exemplifies this integration by embedding its capabilities directly into workflows that developers use daily.
The exam assesses a candidate’s understanding of this integration by presenting scenarios where security features influence or interact with standard development actions. Candidates must demonstrate an appreciation for how security notifications appear in pull request checks, how scans can be automated via GitHub Actions, and how dependency and secret scans integrate into review processes.
By measuring this integration aptitude, the certification reinforces a core DevSecOps principle—security should enhance, not disrupt, development habits.
Prioritization and Risk Evaluation
Professional security work involves prioritizing issues based on real risk—not simply remediating every alert equally. The GH-500 exam indirectly assesses a candidate’s ability to evaluate which issues matter most based on factors such as severity, exploitability, exposure, and potential business impact.
For instance, understanding that a high-severity code scanning finding in a rarely executed module may pose less immediate risk than a moderate vulnerability in a critical authentication path demonstrates professional discernment. Similarly, differentiating between dependencies that require urgent remediation versus those with manageable risk profiles is a key prioritization skill.
Exam scenarios that reflect these judgments measure a candidate’s risk evaluation capability, which goes beyond knowing what a feature does and into how findings should be acted upon strategically.
Cross-Team Collaboration Awareness
Although GH-500 primarily focuses on technical competencies, it also indirectly evaluates an understanding of collaborative workflows common in real development organizations. Security is rarely a standalone responsibility: developers, platform engineers, and security teams must coordinate actions, share insights, and manage alerts collectively.
This collaborative skill is embedded into exam scenarios where candidates are expected to understand how alerts are communicated, how policies affect team members, and how remediation tasks are assigned and tracked. Recognizing the importance of these coordination patterns reflects not only technical capability but also organizational empathy—an awareness of how security functions operate within team dynamics.
GitHub Advanced security Certification (GH-500) Preparation Guide
Preparing for the GitHub Advanced Security Certification (GH-500) goes beyond exam tactics—it requires developing the mindset of a practitioner who understands how security is embedded into modern development workflows. The exam is intentionally designed to validate applied knowledge of GitHub Advanced Security (GHAS) rather than surface-level familiarity with tools or terminology. This section focuses on how candidates should think while preparing, and how to align learning habits with the way the exam evaluates real-world security decision-making.
Adopt an Application-First Security Perspective
- GH-500 assesses your ability to secure code as it moves through GitHub, not in isolation. The exam expects candidates to reason through scenarios involving repositories, pull requests, CI/CD pipelines, and automated security checks.
- Your preparation mindset should reflect this by treating GitHub as the central security control plane. Instead of studying features independently, focus on how they protect applications throughout the software development lifecycle—from commit to deployment. This approach mirrors how GHAS is used in production environments and aligns closely with the exam’s structure.
Think Like a DevSecOps Practitioner, Not a Tester
The GH-500 exam indirectly evaluates how well you understand the shared responsibility between developers, security teams, and platform engineers. Security decisions are rarely isolated; they are influenced by workflow efficiency, developer experience, and organizational policies. A strong preparation mindset involves thinking like a DevSecOps professional who must:
- Integrate security without disrupting development velocity
- Interpret security findings in context
- Decide when automation is appropriate and when manual review is necessary
This perspective helps candidates approach scenario-based questions with practical judgment rather than rigid rule-following.
Prioritize Understanding Over Feature Recall
- While the exam covers multiple GHAS capabilities, it does not reward rote memorization of feature definitions. Instead, it emphasizes why a feature exists, when it should be used, and how it influences security outcomes.
- For example, understanding how code scanning results are surfaced, triaged, and acted upon is more valuable than simply knowing what code scanning does. Preparing with this mindset ensures you can reason through unfamiliar scenarios rather than relying on pattern recognition alone.
Build Context Through Hands-On Exploration
- The official exam guidance strongly encourages experiential learning. GH-500 assumes familiarity with how GHAS behaves in real repositories, including how alerts are generated, displayed, and resolved.
- Hands-on exposure helps candidates develop intuition—an essential skill for interpreting exam scenarios. When you’ve seen how security findings appear in pull requests or dashboards, it becomes easier to reason about expected outcomes in exam questions.
Recommended Learning Resources for GH-500 Preparation
To support the right preparation mindset, candidates should rely on authoritative and practice-oriented resources that reflect the actual scope of the exam.
Official Microsoft Learn Resources
Microsoft Learn provides the most accurate and exam-aligned material for GH-500 preparation. These resources define the certification scope, skill expectations, and assessment philosophy:
- GitHub Advanced Security Certification Overview
- Explains certification intent, audience, and validated skills.
- GH-500 Official Study Guide
- Breaks down exam domains and outlines the knowledge areas candidates are expected to master. This guide is essential for aligning preparation with exam objectives.
Further, third-party platforms can complement official materials by reinforcing concepts through structured explanations and scenario-based practice:
- GH-500 Tutorial
- Offers exam-focused explanations that help contextualize GHAS features and reinforce applied understanding.
Align Learning Resources With Exam Intent
An effective preparation mindset involves selective resource usage. Instead of consuming as much content as possible, focus on resources that emphasize:
- Real-world GitHub security workflows
- Interpretation of security findings
- Integration of security into CI/CD pipelines
Common Misconceptions About the GH-500 Exam
In preparing for the GitHub Advanced Security Certification (GH-500), many aspirants bring assumptions shaped by traditional certification exams. However, GH-500 is purposefully structured around real-world application security scenarios directly tied to GitHub Advanced Security (GHAS) usage. Misunderstandings about the exam’s intent, format, and expectations can derail preparation if not addressed early. Drawing on official certification guidance and exam content outlines, this section clarifies prevalent misconceptions and reframes them to align with how GH-500 is designed and assessed.
Misconception 1: GH-500 Is Primarily a Tool-Feature Recall Test
A widespread belief is that success on GH-500 depends on memorizing feature names, settings, or menu locations within GitHub Advanced Security. In reality, the exam goes far beyond simple recall. The official study guide emphasizes applied understanding—how features function in live workflows, how security findings are interpreted, and how configurations influence security outcomes.
For example, rather than merely knowing that CodeQL performs static analysis, the exam expects candidates to understand how code scanning integrates into workflows, how scan results impact development decisions, and how to tune analyses to manage false positives effectively. Preparing with this applied perspective ensures that your understanding extends beyond checklists to actionable competence.
Misconception 2: Memorizing Documentation Will Guarantee Success
Another misconception is that reading official GitHub documentation end-to-end will suffice for exam preparation. While documentation is valuable for understanding individual features, the GH-500 exam evaluates decision-making in context. According to official guidance, the certification assesses how you would use GHAS features to support security throughout the software development lifecycle—not simply whether you can recite how a capability works.
For instance, understanding documentation on dependency review is helpful, but candidates must also be able to interpret alerts, weigh remediation choices, and integrate dependency data into development risk assessments. This requires cultivating analytical judgment rather than rote memorization.
Misconception 3: Extensive Theory Is What the Exam Focuses On
In contrast to some security certifications that prioritize abstract security principles, GH-500 focuses primarily on practical application within GitHub. The assessment evaluates your ability to implement and interpret GitHub Advanced Security workflows—how security checks integrate with pull requests, how alerts are surfaced and prioritized, and how automation supports secure coding practices.
While a baseline understanding of security principles is certainly useful, the exam is not centered on abstract theory. It emphasizes contextualized scenarios that simulate how security features are actually used within teams and pipelines.
Misconception 4: GH-500 Is Only for Security Engineers
Many candidates assume that GH-500 is exclusively for dedicated security professionals. In truth, the certification is designed for a broad audience that includes developers, platform engineers, DevOps professionals, and administrators—anyone involved in maintaining security within GitHub workflows.
The exam’s content spans secret scanning, code analysis, dependency security, and practical remediation strategies—domains that intersect with development and DevOps responsibilities as much as with traditional security roles. This reflects the shared responsibility model inherent in modern DevSecOps practices, where security is integrated throughout development rather than siloed.
Misconception 5: Passing GH-500 Means Mastering Every GHAS Feature
A related misconception is that success on the GH-500 exam means becoming an expert on every GitHub Advanced Security capability. Official certification guidance indicates that mastery of each feature in isolation is less important than understanding how security features combine within workflows to address real risks.
For example, secret scanning and dependency alerts might be activated independently, but their findings often influence shared remediation priorities or governance decisions. The exam evaluates how candidates prioritize, coordinate, and respond to these findings—skills that reflect professional judgment rather than encyclopedic tool knowledge.
Final Thoughts
The GitHub Advanced Security Certification (GH-500) is designed to validate practical security skills that reflect how modern development teams work inside GitHub. Rather than testing isolated knowledge, the exam focuses on how effectively you can apply security controls, interpret findings, and make informed decisions within real development workflows.
Approaching preparation with a hands-on, workflow-oriented mindset not only improves exam readiness but also builds skills that translate directly into day-to-day DevSecOps responsibilities. When studied with this perspective, GH-500 becomes less of a certification milestone and more of a professional capability upgrade.